When a bug discovered in the widely-used cryptography library OpenSSL was disclosed on April 7, Calvin Information Technology, along with thousands of other I.T. and software organizations, rushed to respond to the vulnerability. The bug affected a number of services that Calvin uses internally and interfaces with.
OpenSSL is the most popular library implementing the SSL/TLS protocol, a protocol for providing secure connections over the Internet by encrypting data. As open-source software distributed under an Apache-style license, it is available for free.
According to an April 2014 survey by Netcraft, 66 percent of active websites use either Apache or Nginx web server software, both of which use OpenSSL for security.
The Heartbleed bug is the result of a “relatively mundane coding error,” according to Johns Hopkins University professor Matthew Green. The mistake lies in a “heartbeat” extension to TLS which allows computers to maintain a secure connection by periodically sending messages to check if the other computer is still there.
Heartbeat messages contain a request for a response from the other computer, but the (unpatched) software fails to check the length of the requested response. This lack of a bounds check on the request means that an attacker can request up to 64 kilobytes of private memory, which can contain cryptographic keys, users’ passwords and sensitive data.
Attackers could use information stolen through Heartbleed to gain access not only to users’ accounts, but also to the web servers themselves. Attackers could decrypt encrypted data sent to a server or impersonate a website. This vulnerability is particularly dangerous because attacks leave no trace in the system.
Netcraft found that 17.5% of websites using SSL, about half a million total, had the heartbeat extension enabled, leaving them vulnerable.
On April 11, Bloomberg reported that two anonymous sources claimed that the NSA exploited Heartbleed for two years. Both the NSA and the White House denied the allegations.
A statement posted on the blog of the Office of the Director of National Intelligence read, “NSA was not aware of the recently identified vulnerability in OpenSSL, the so-called Heartbleed vulnerability, until it was made public in a private sector cybersecurity report. Reports that say otherwise are wrong.”
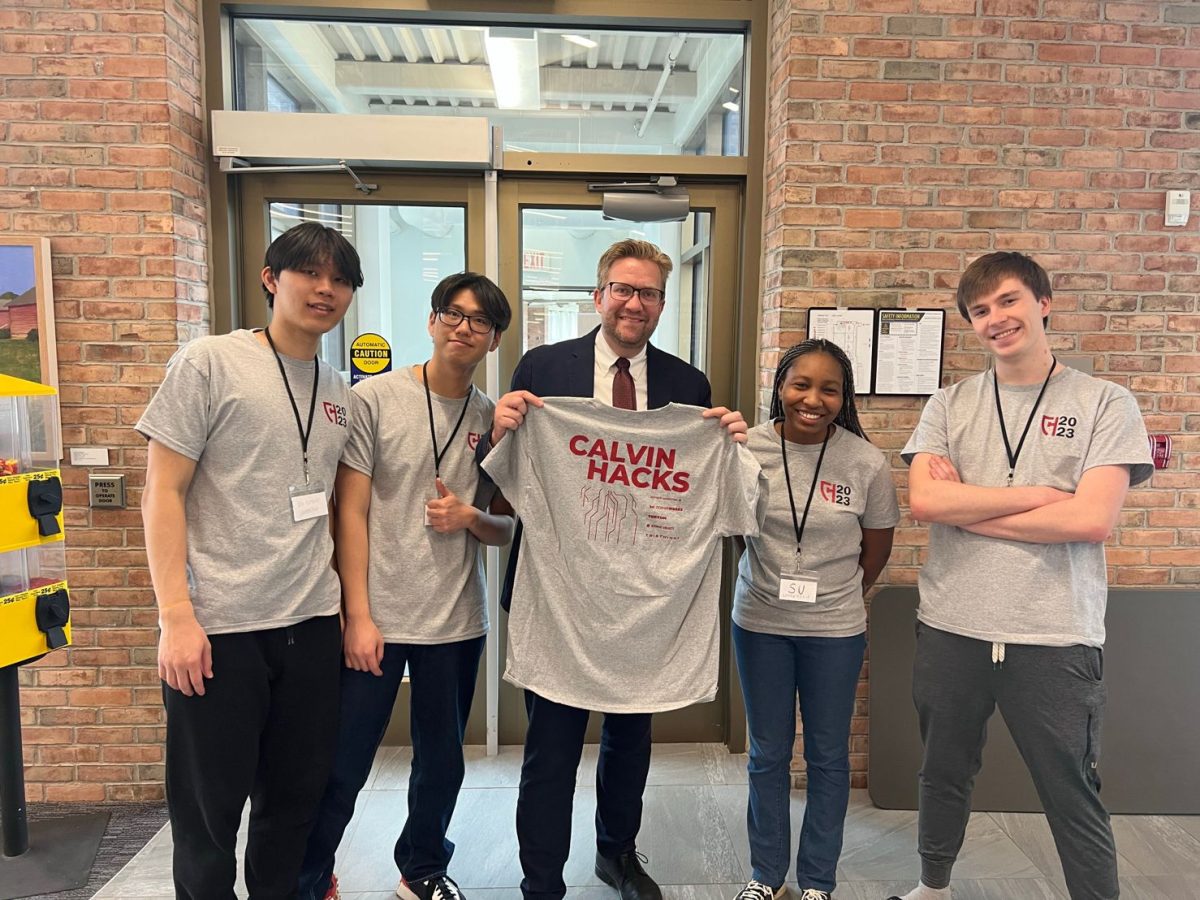
Michael Mandeville, head of Student Technology Services, wants to clear up confusion surrounding the bug. “It’s not even close to a virus,” said Mandeville, referring to concerns reported by help desk patrons. “This is going to be scapegoat for another year.”
“How do we communicate about it without freaking people out?” asked Mandeville. “There just happens to be this little hole,” says Mandeville, describing the vulnerability exposed by the bug. A patch came in short order. Mandeville praised Calvin’s software vendors, most of whom “were quick to respond.”
Regarding enforcing a mandatory password change, Mandeville labelled it the “hardest decision made.” The major factor was that Google, whose services were vulnerable to Heartbleed, provides StudentMail.
While there is no evidence of any security breaches at Calvin enabled by Heartbleed, the password change was “mostly a peace of mind thing,” said Mandeville.
According to an investigation by the information security firm Sucuri, Inc. published April 17, all of the Alexa Top 1,000 websites have been patched, but 2 percent of the Alexa Top 1,000,000, or 20,320 websites, were vulnerable.